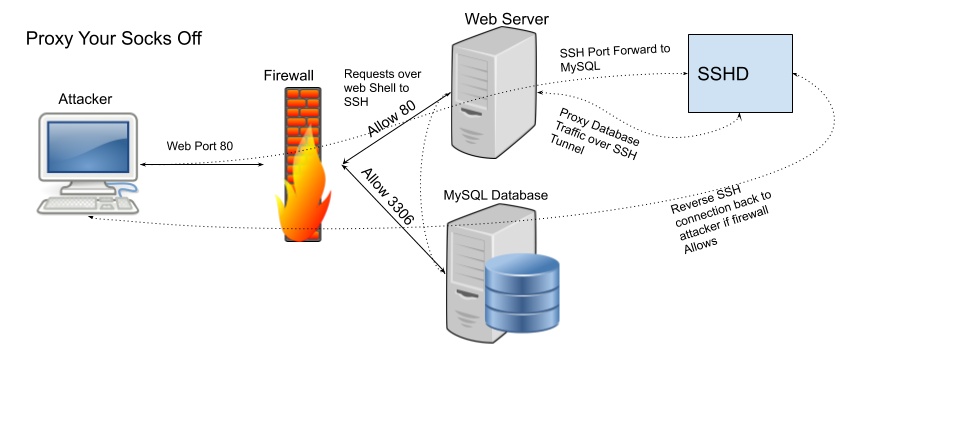
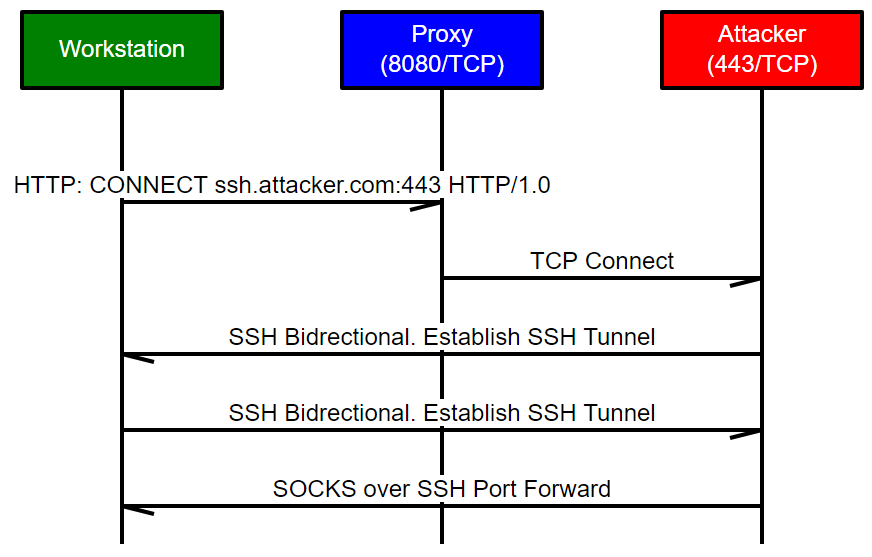
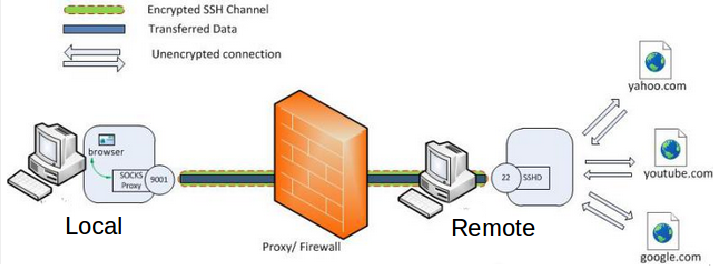
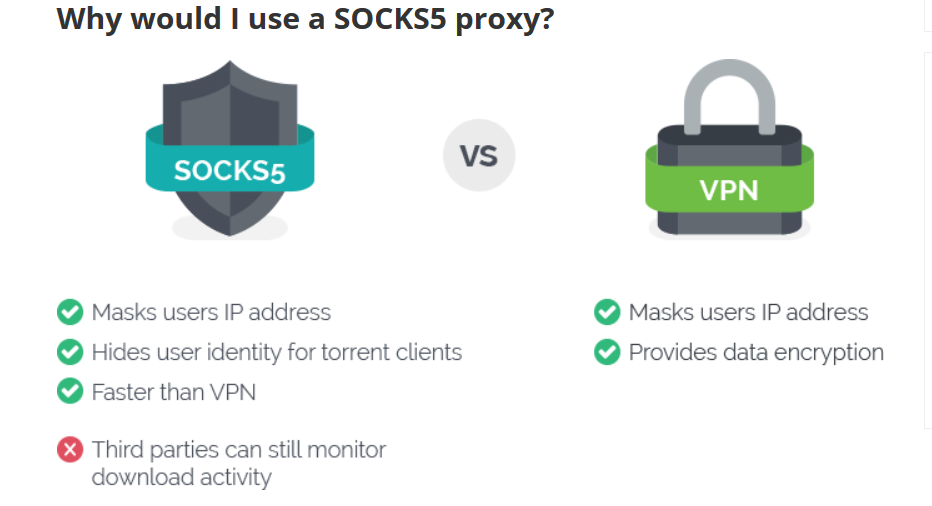
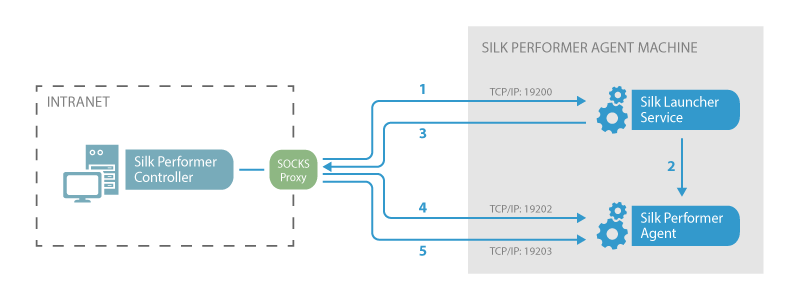
Offensive Security Guide to SSH Tunnels and Proxies | by Russel Van Tuyl | Posts By SpecterOps Team Members
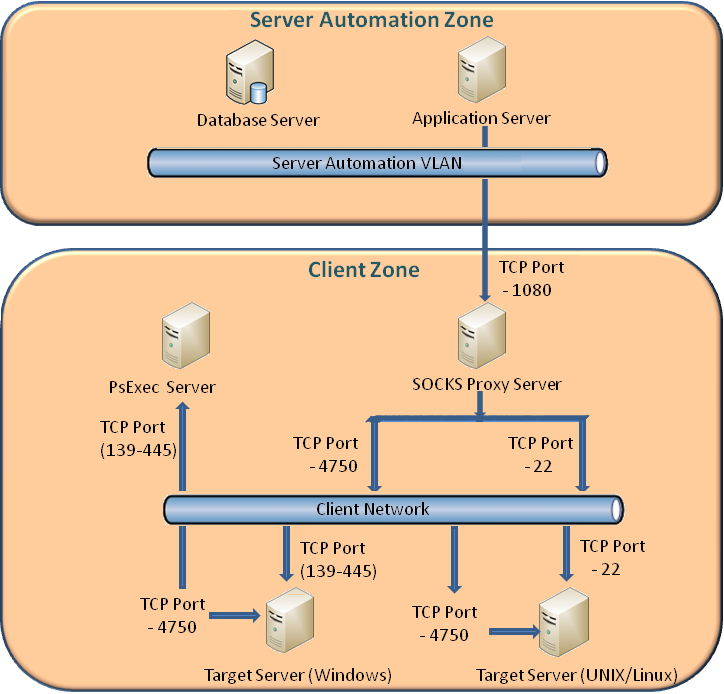
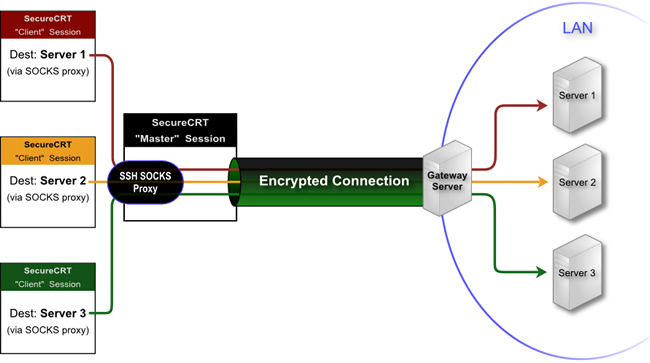
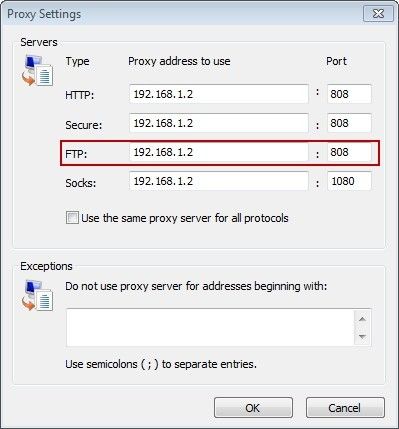
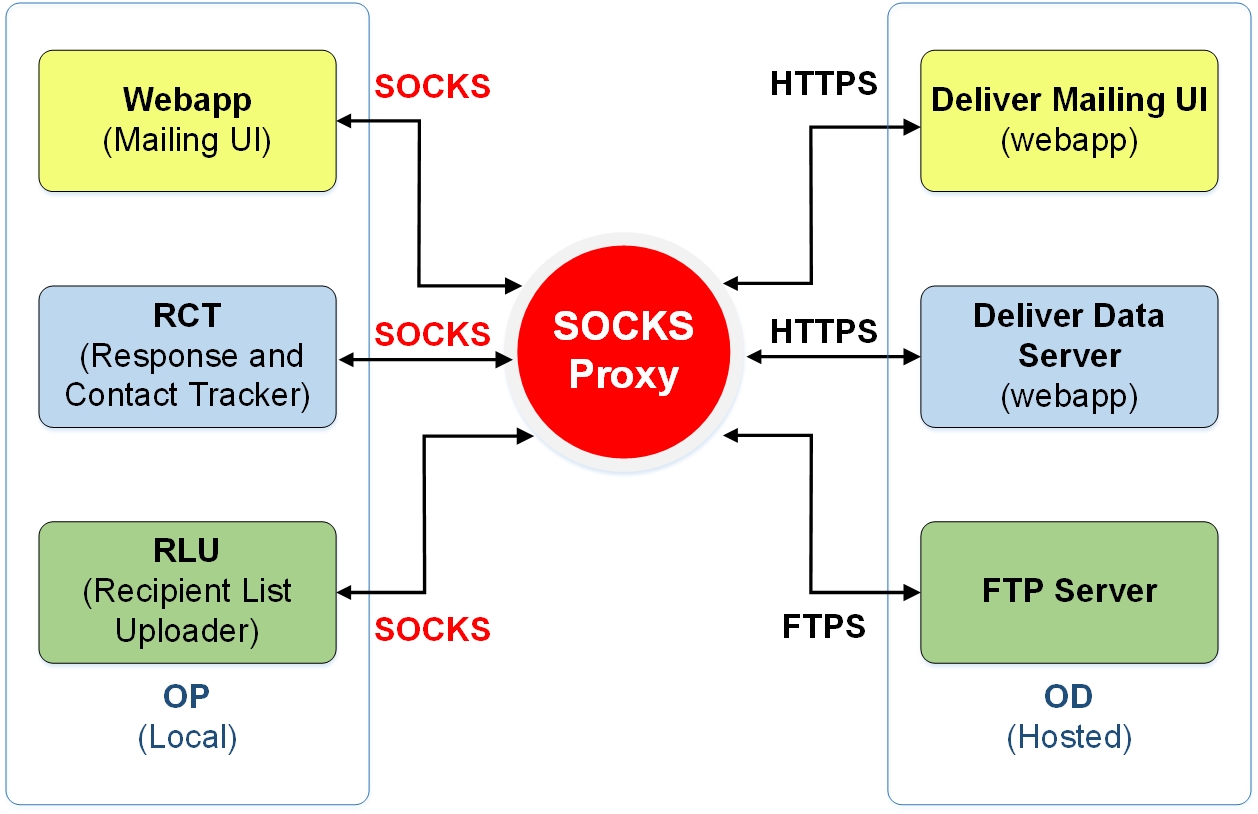
Sample setup for the target servers located behind a SOCKS proxy server - Documentation for TrueSight Server Automation 21.3 - BMC Documentation